Building Secure CI/CD Pipelines — Practical Checklist
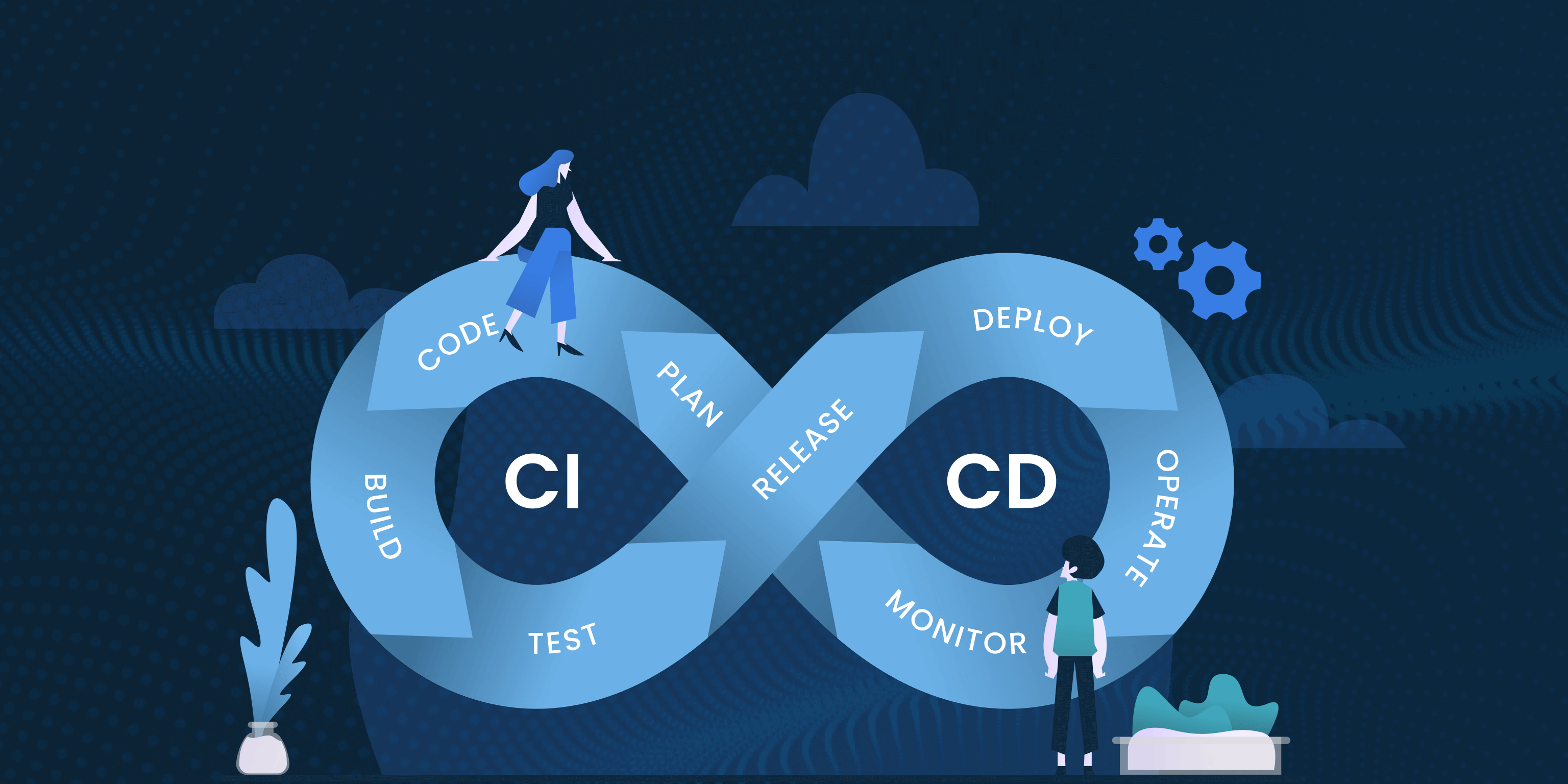
CI/CD pipelines are the backbone of modern software delivery. But if left unsecured, they become one of the biggest attack surfaces. Here’s a practical, actionable checklist to secure your end-to-end pipeline.
Why CI/CD security matters
Your pipeline holds your code, secrets, build artifacts, and deployment permissions. A compromised CI/CD system gives attackers the keys to your entire infrastructure. Securing pipelines is no longer optional — it’s a core DevSecOps responsibility.
Checklist #1 — Secure your source code & SCM
- Enforce MFA on GitHub, GitLab, Bitbucket accounts.
- Restrict branch permissions (main/master protected, mandatory PR reviews).
- Enable secret scanning to detect leaked API keys.
- Remove personal access tokens and move to OIDC authentication.
Checklist #2 — Secure CI runners
- Avoid shared runners for production workloads.
- Use ephemeral runners so each build starts clean.
- Limit network access from CI to production environments.
- Scan Docker images used as runners for vulnerabilities.
Checklist #3 — Secrets management
- Use a secrets manager like AWS Secrets Manager, Vault, or Doppler.
- Avoid storing secrets in CI variables unless encrypted + short lived.
- Rotate secrets automatically with lifecycle policies.
- Use OIDC federation instead of long-lived cloud credentials.
Checklist #4 — Secure build artifacts
- Use artifact signing (Sigstore, Cosign, SLSA-compatible builds).
- Scan artifacts using SCA (Software Composition Analysis).
- Store artifacts in access-controlled registries.
- Implement SBOM generation to track dependencies and licenses.
Checklist #5 — Secure deployments
- Use least-privilege IAM roles for deploy jobs.
- Enable approval workflows for production pushes.
- Deploy through APIs instead of SSH.
- Implement rollback automation with health checks.
Checklist #6 — Monitoring, logging & audits
Track and audit everything that touches your pipeline:
- Failed login attempts
- Pipeline modifications
- Access to secrets or cloud roles
- Changes to deploy configurations
- Artifact download history
Quick Start — Practical first steps
- Move to OIDC authentication for cloud deployments.
- Add SAST + SCA to each pull request.
- Harden runners and block egress traffic by default.
- Roll out a secrets-rotation policy every 90 days.
- Adopt SLSA Level 2 or higher for build integrity.
A secure CI/CD pipeline isn’t built once — it’s maintained continuously. Treat pipeline security as part of your SDLC, automate as much as possible, and adopt DevSecOps practices early to safeguard your entire delivery chain.